by Nelson | Apr 24, 2026 | DIGITAL TRANSFORMATION
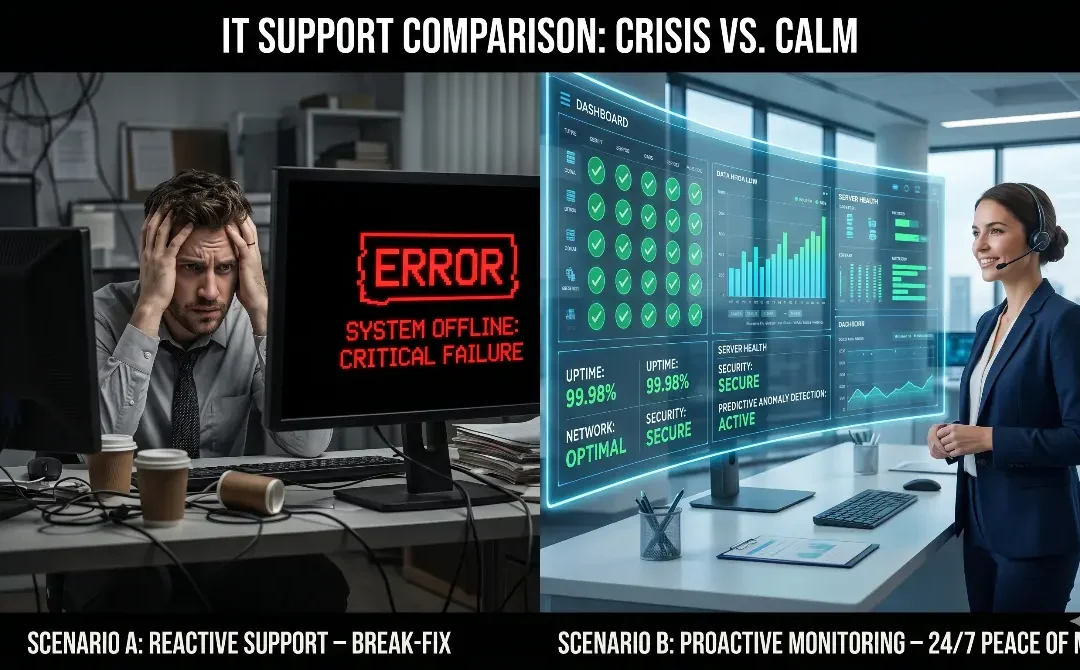
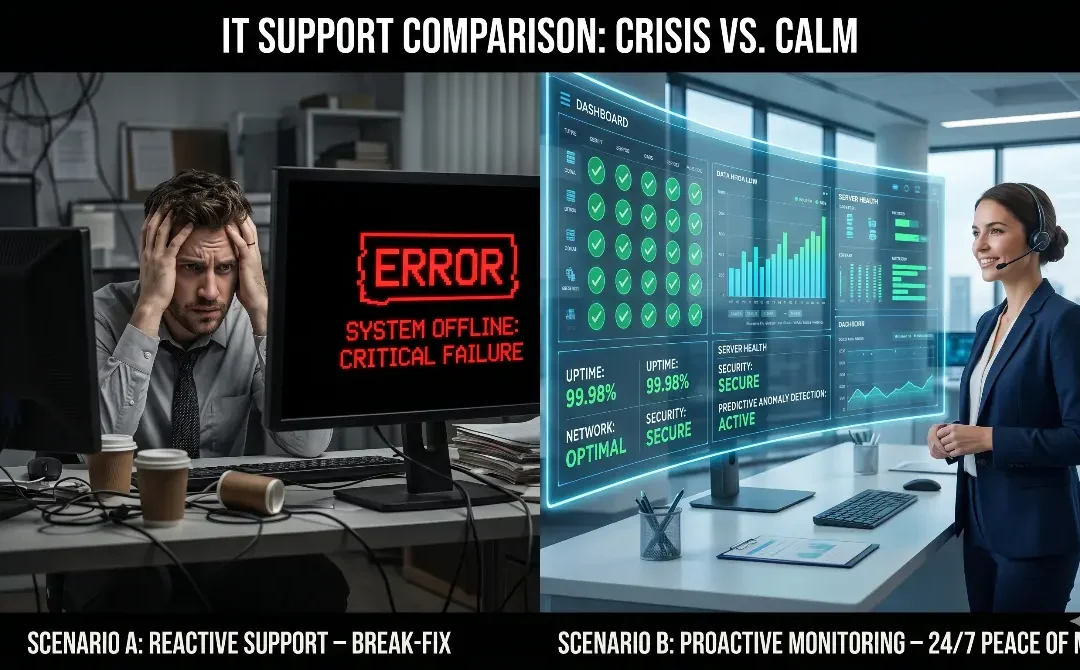
Imagine two companies of the exact same size, in the same industry, and with the same initial IT budget. Company A calls for support only when something has already stopped working: the server is down, the network has no connection, or the electronic billing system is...

by Nelson | Apr 17, 2026 | CYBERSECURITY
60% of SMEs that suffer a critical cyberattack close their doors within 6 months. A ransomware attack (malicious software that “kidnaps” your data and demands a financial ransom to return it) is currently the number one threat to mid-sized companies...

by Nelson | Apr 10, 2026 | DIGITAL TRANSFORMATION
Introduction Not all technology service providers are created equal. The market is full of companies offering seemingly low rates, but when a critical hour strikes, they respond with a single, inexperienced technician. Others impose contracts full of “fine...

by Nelson | Apr 3, 2026 | CYBERSECURITY, DIGITAL TRANSFORMATION
Introduction In many small and medium-sized businesses, the IT department grows purely reactively. What starts as basic support (someone fixing printers and setting up emails) ends up becoming a critical bottleneck for the entire operation. When incidents pile up,...